HOW CLOUDFLARE SPEED UP AND PROTECT YOUR WEBSITE – PART 2.
Cloudflare SSL : 3 security levels
You are maybe aware than https will become a standard for all websites in the next few years, because it's encrypt the connection between your visitors and your website, making it safer for them.
With Cloudflare you have 3 level of SSL security. The first one name "Flexible" will not require you to install SSL on your server, acting as a proxy Cloudflare will only use SSL between your visitors and their servers. If your visitors will be able to navigate on your website with an encrypted connexion, this configuration is not really secured as anyone can intercept data between cloudflare and your server. This kind of attack are named "man-in-the-middle".
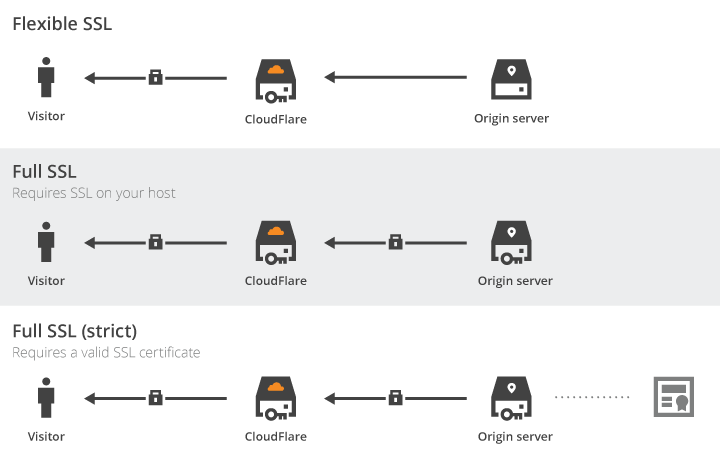
The second level of SSL with cloudflare will require for you to setup a valid SSL certificate. That doesn't mean you will have top pay for that. You can use letsencrypt to secure your server, and then use cloudflare in "Full SSL" to have this time a totally secured connection between your server and your visitor.
For me, if you want to use SSL, the Full SSL is the minimum to setup. The flexible mode is really useless as it doesn't protect properly your visitors. And the next level the Full "Strict" will require a valid certificate, signed by a trusted authority. This also require to use the HSTS, which is a mechanism to force a browser to use ssl on a website for a fixed period. That mean, if your website don't use SSL all the time, any modern browser will block the connection to protect the user. So when you are using HSTS, you have to be sure than the SSL certificate will always be valid. This is the most secure level to setup with Cloudflare, but it should not be required if you don't need a very high-level of security to process credit card or other transaction.
How to use https instead of http ?
At first you have to be sure than all the content available on your website can be delivered to your visitors using https. That mean you will have to check your if there are not some external css or javascript which is process using http. The easiest way to have files compatible under https is to link all your assets like that :
<link rel="stylesheet" href="//thedomain.com/css/yourtheme.css" type="text/css" />But even with this method, if a file could not be processed under https, it will be blocked by the visitor's browser and it will not see the green padlock in his browser. So check properly the sources of your assets, there are a lot of wordpress themes which still request google fonts using http.
So now, we will use letsencrypt to get a free SSL certificate. But before, if you are already using Cloudflare, you will have to disable the proxy mode, because to validate your domain ownership, letsencrypt create a small file named ".well-known" on your webspace and try to access it by resolving your IP. That mean if you are using Cloudflare, it will try to validate the proxy and it will fail.
For Apache on Ubuntu/Debian :
apt-get install git
git clone https://github.com/letsencrypt/letsencrypt /opt/letsencrypt
cd /opt/letsencrypt
## you can use it also for a subdomain like -d subdomain.example.com
./letsencrypt-auto --apache -d example.com -d www.example.com
Let's do the same with Nginx
apt-get install git
git clone https://github.com/letsencrypt/letsencrypt /opt/letsencrypt
cd /opt/letsencrypt
./letsencrypt-auto certonly --webroot -w /var/www/example.com/htdocs/ -d example.com -d www.example.com --email contact@example.com --text --agree-tos
## then to activate it with Nginx, add this on your server { } config
listen 443 ssl http2;
ssl on;
ssl_certificate /etc/letsencrypt/live/example.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/example.com/privkey.pem;
## and reload nginx
nginx -t && service nginx reload
## And if you want to force http to https
nano /etc/nginx/conf.d/force-ssl.conf
## then add
server {
listen 80;
server_name example.com;
return 301 https://example.com$request_uri;
}
And if you want to renew automatically your certificate, it's not very hard
## to renew automatically your certificate
sudo crontab -e
## then enter
30 2 * * 1 /opt/letsencrypt/letsencrypt-auto renew >> /var/log/le-renew.log
## to update letsencrypt
cd /opt/letsencrypt
sudo git pull
So, you have now a valid SSL certificate, and you should see the small green padlock in your browser. And you can now use Cloudflare in "Full SSL" and that mean your website should be safer for your visitors.
And the last level of security with Cloudflare is now really easier, because it was required to buy an SSL certificate in the past, it's now over because Cloudflare will issue it for you, and it's totally free. So you will have to go to your Cloudflare account in the crypto tabs of your domain. And in the section Origin certificates, you will be able to create a certificate, and then to install it on your server by following the tutorials available for each web server.
But if you are using a control panel like Plesk, it doesn't work the same than with a classic web server. It will require to create a CSR (Certificate Signing request) like if you are planning to buy a certificate. But you will just have to enter your personal details, and then to click on request to have the CSR and you private key. Then you just have to download the .pem file and to open it will a text editor to copy the details at Cloudflare.
And it will give you the certificate to add in your control panel. BUT you will also have to enter the Cloudflare root certificate which is the authority to validate it. It take me few hours to find the post about it on the Cloudflare knowledge base : Root Certificate Cloudflare
So you should have your CSR on your control panel, and you private key, your certificate and the root authority, and you will just have to copy them in the text area available to have a real certificate, validated by an authority. It will allow you to use the Cloudflare "Full SSL (Strict)" mode which is the last security level with Cloudflare.
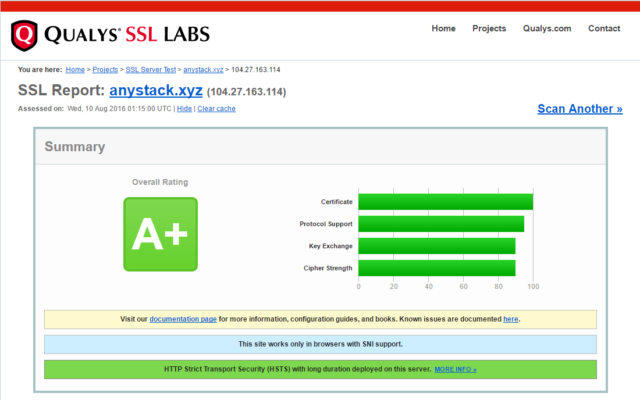
So all the data between your visitors and your website will be fully encrypted, and you should have the best result at SSLabs when you will test the security level of your SSL server.
And when the https was slower than http few years ago, because it require an initial handshake during the first connection, it include now several features and the biggest one is the HTTP2.
But I will write another post about that later, because it will require a complete article.